Protection against (firesheep) session hijacking
Last month, a simple firefox extension called FireSheep caused a slight panic amongst web developers. FireSheep makes it dead simple to hijack a user session with just one click. Even a 10 year old could take over your Facebook session with a single mouse click.
Don’t worry: all shops on SolidShops.com are protected against session hijacking. We wanted to put this blog post out there only to inform web developers and end users about the problem of session hijacking.
Let me explain in short what the problem is and why any other web application out there should also protect its users from session hijacking.
The problem of session hijacking
Normally, when you log in to a website, the website will put a session cookie on your computer so that the application or website knows who your are. Without this cookie, it would be impossible to remember that you have logged in earlier and the application would ask you to login again and again for every page you requested.
There are of course other mechanisms for doing session management, but using cookies is by far the most widely used approach. Now, the real problem is that this session cookie travels over a protocol called HTTP, the standard protocol a web server uses to communicate with you as a surfer.
Anyone with access to the network you are on (it doesn’t matter if this is cable or wifi) could sniff this traffic on your network. Simple put, people can eavesdrop on all data that is being sent in the clear over a network. Especially public wifi hotspots are places where a malicious person could easily tap into ones data traffic.
When a person is able to sniff your session cookies, that person could impersonate you and use a tool like FireSheep to log in as you withas little as one mouse click.
The solution against session hijacking
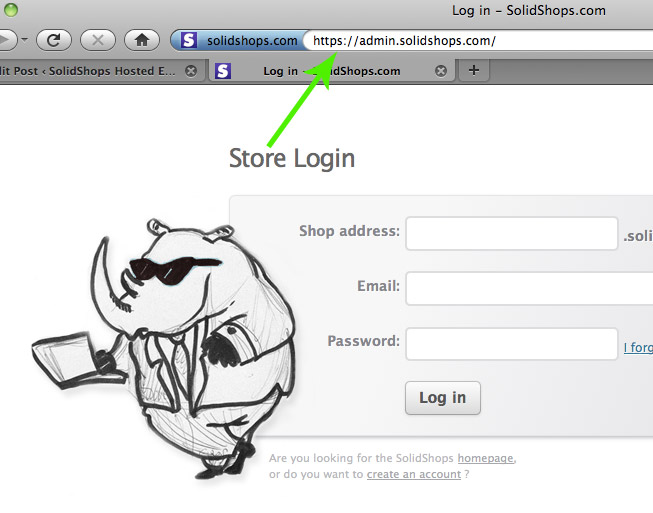
The solution to keep someone from stealing your session cookie is to use an encrypted connection, something like a special code you use to talk to the web server. This can easily be accomplished by using HTTPS instead of normal HTTP. Just check at the top of your web address bar what the url is. If it says “http://”, all traffic is sent in the clear. If it says “https://” then it becomes much harder for someone to sniff your data and sessions.
We are using full HTTPS on the admin side of your SolidShops account, so your login sessions are safe there. Bear in mind that it’s important not only to protect the login screen, but also to encrypt the complete session from that point on. If you would only protect the login screen and then move further in your application over normal HTTP, your session data will be exposed again.
Of course it’s not necessary to protect all your websites and web pages by HTTPS. A simple portfolio website for example that doesn’t expose sensitive data doesn’t have to be on HTTPS. A hacker isn’t interested in that kind of non-sensitive data.
So again … relax, your SolidShops account is safe. But in order for the Internet to become a safer place, anyone should demand HTTPS support on a web application where a login is necessary or where sensitive data is processed. If you are still using web applications where you login over normal HTTP traffic, know that you are possible exposing too much of yourself, and ask the website owner to take precautions for its users.
Keep it safe everyone and enjoy the holidays!
Let's get social shall we?
We'd love to know what you think. Join the conversation about your hosted e-commerce solution.